390 reads
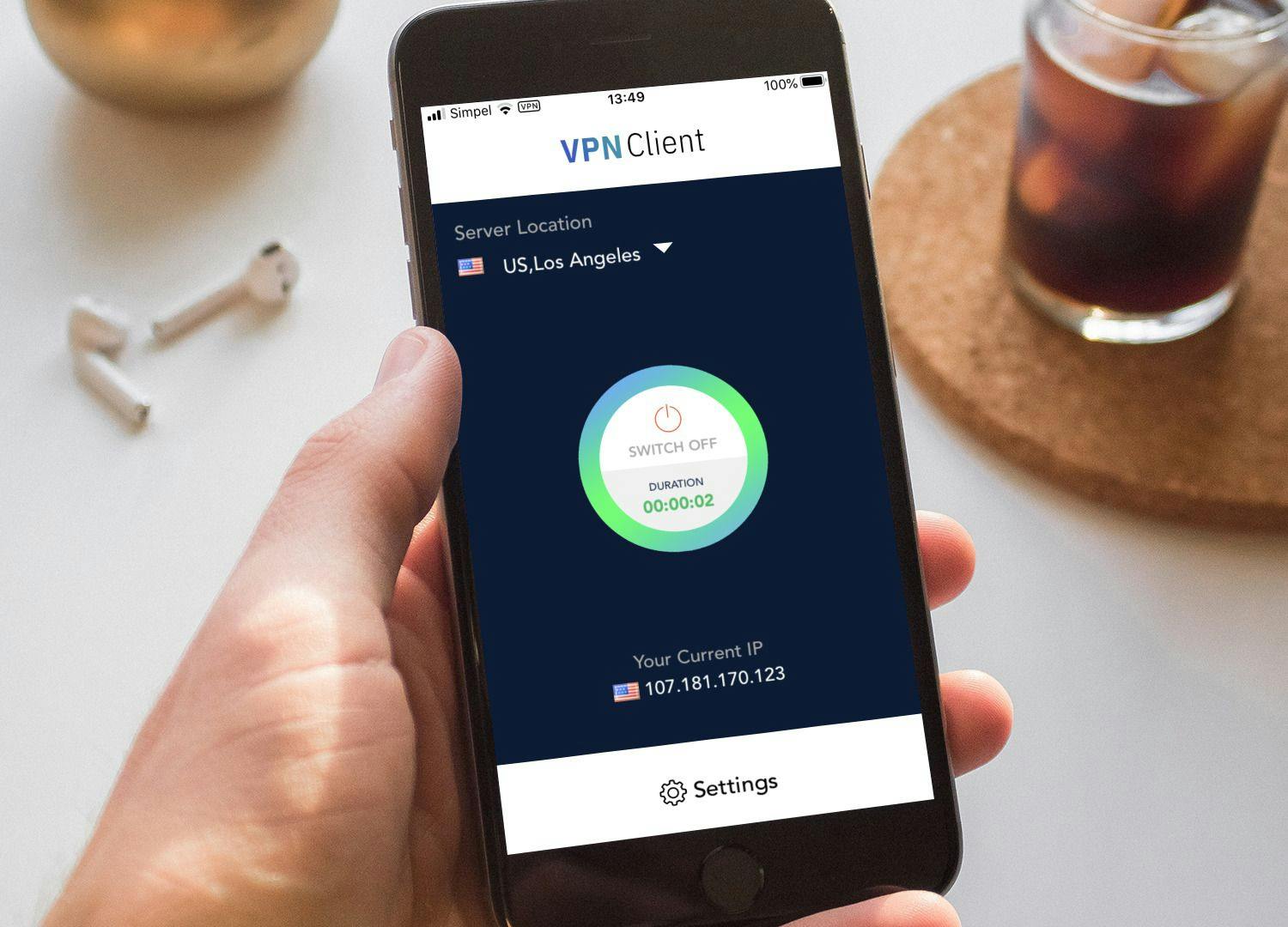
5 Secure Technologies That Protect Online Traders
by
April 18th, 2022
Audio Presented by
Always interested in the latest tech, especially blockchain and cybersecurity.
About Author
Always interested in the latest tech, especially blockchain and cybersecurity.
Comments
TOPICS
THIS ARTICLE WAS FEATURED IN
Arweave
ViewBlock