137 reads
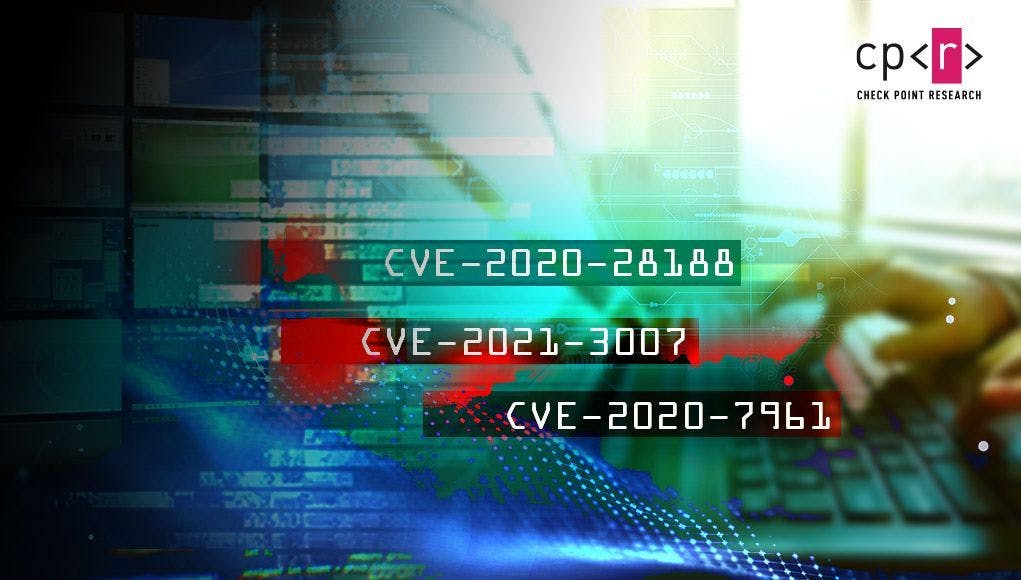
What Vulnerabilities FreakOut Takes Advantage of for Creating a Botnet
by
September 4th, 2021

Welcome to the Future of Cyber Security. Providing solutions across all vectors to prevent 5th generation cyber attacks.
About Author
Welcome to the Future of Cyber Security. Providing solutions across all vectors to prevent 5th generation cyber attacks.