11,695 reads
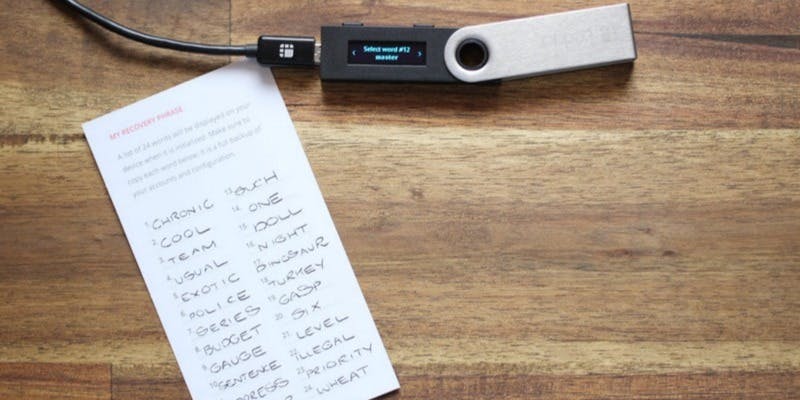
How to Keep Your Seed Phrase Safe?
by
August 16th, 2019
Audio Presented by

Co-founder of DOITONG & HashEx. Expert in AI, blockchain security, and product strategy.
About Author
Co-founder of DOITONG & HashEx. Expert in AI, blockchain security, and product strategy.