328 reads
Computer Trojan Attacks: Nature, Development and Prevention
by
July 26th, 2022
Audio Presented by
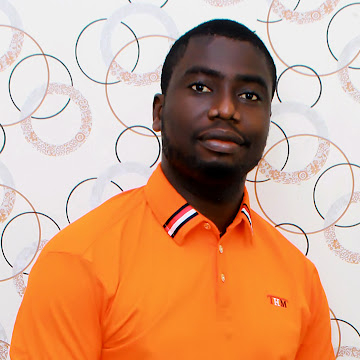
Tech enthusiast and freelance writer. Columnist in many other authoritative publications.
About Author
Tech enthusiast and freelance writer. Columnist in many other authoritative publications.
