307 reads
How to Manage Exchange Online DNS Records for SPF, DKIM, and DMARC with PowerShell
by
October 1st, 2021
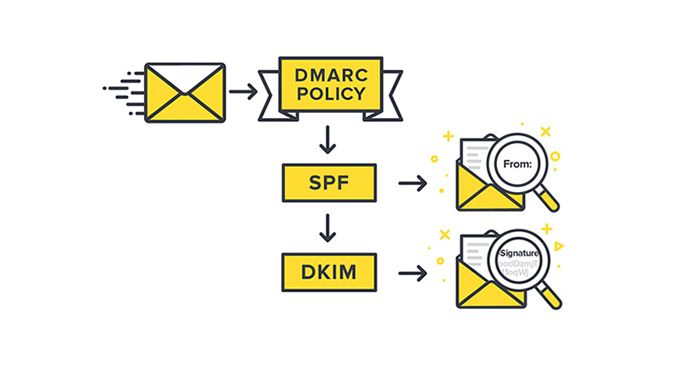
This company is providing you Securing your email & domain with SPF, DKIM and DMARC related Blog ·
About Author
This company is providing you Securing your email & domain with SPF, DKIM and DMARC related Blog ·
