578 reads
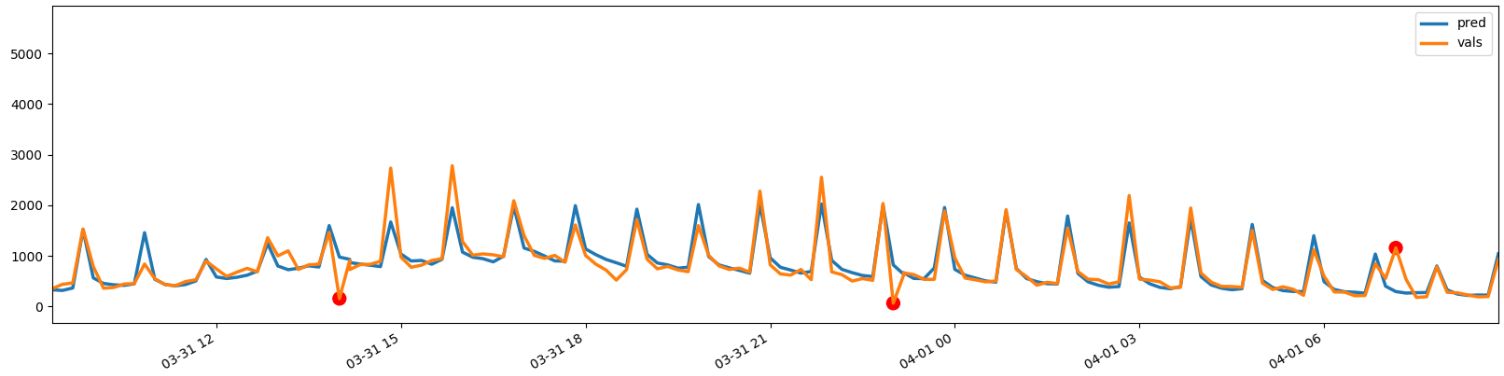
Building a Neural Network to Detect Ad Fraud
by
July 16th, 2020
Comments
TOPICS
THIS ARTICLE WAS FEATURED IN
Related Stories
A Closer Look at Online/Digital Fraud
@clickme
May 03, 2022
A Closer Look at Online/Digital Fraud
@clickme
May 03, 2022