739 reads
Build a Private Cloud Storage Service on the Blockchain
by
January 14th, 2022
Audio Presented by
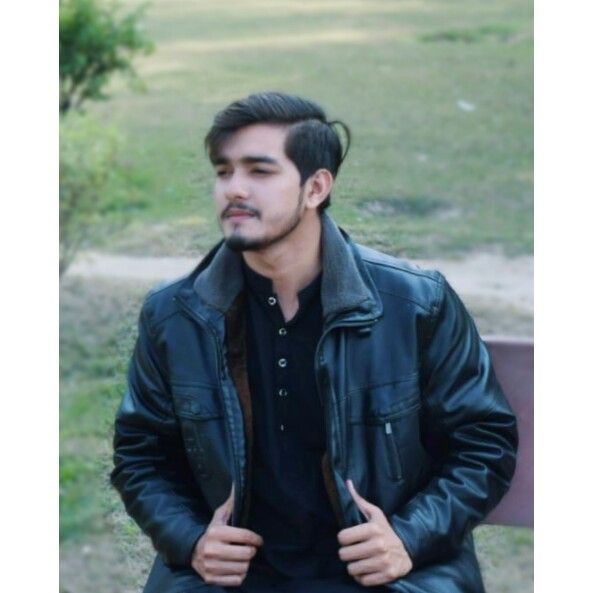
Atiq Malik is a technology web content creator and a cloud computing enthusiast working with cloud computing.
About Author
Atiq Malik is a technology web content creator and a cloud computing enthusiast working with cloud computing.
