10,798 reads
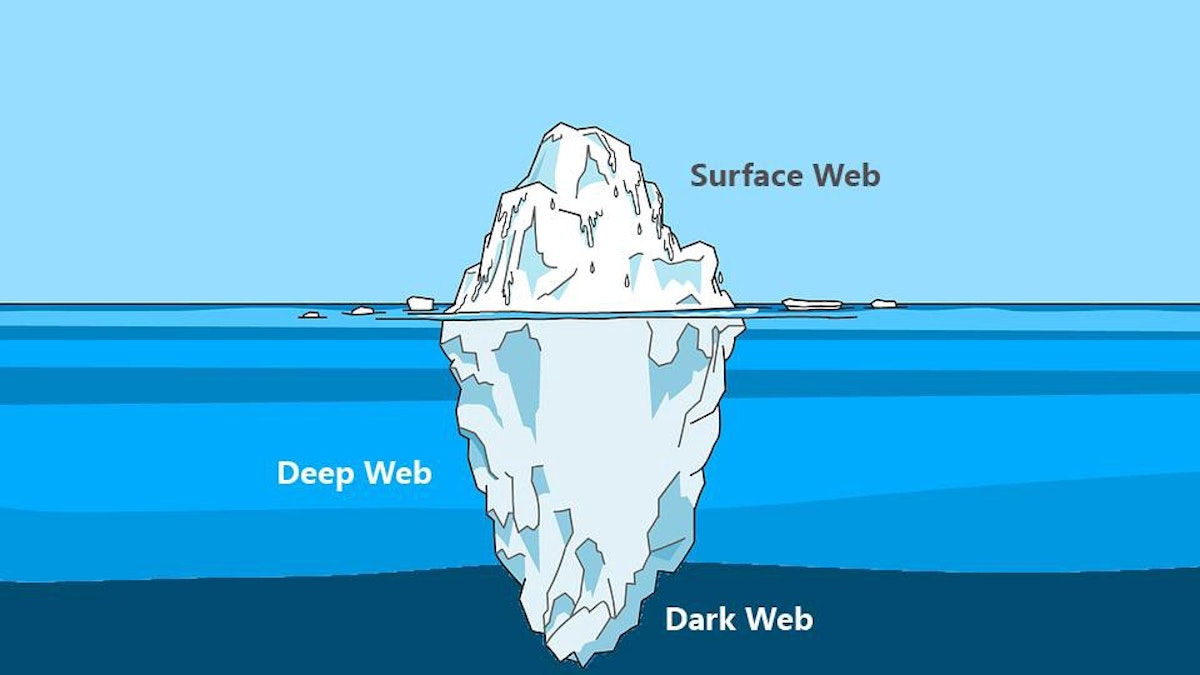
Understanding the Deep & Dark Web

Too Long; Didn't Read
The misinterpretation of terms such as the Darknet, Dark Web, and Deep Web has always been prevalent. In the cybersecurity world, these terms have come to light with the exposure of techniques used by cybercriminals to communicate, collaborate, and participate in malicious activities. This report aims to help in understanding these terms and shed light on relevant topics within them.L O A D I N G
. . . comments & more!
. . . comments & more!