230 reads
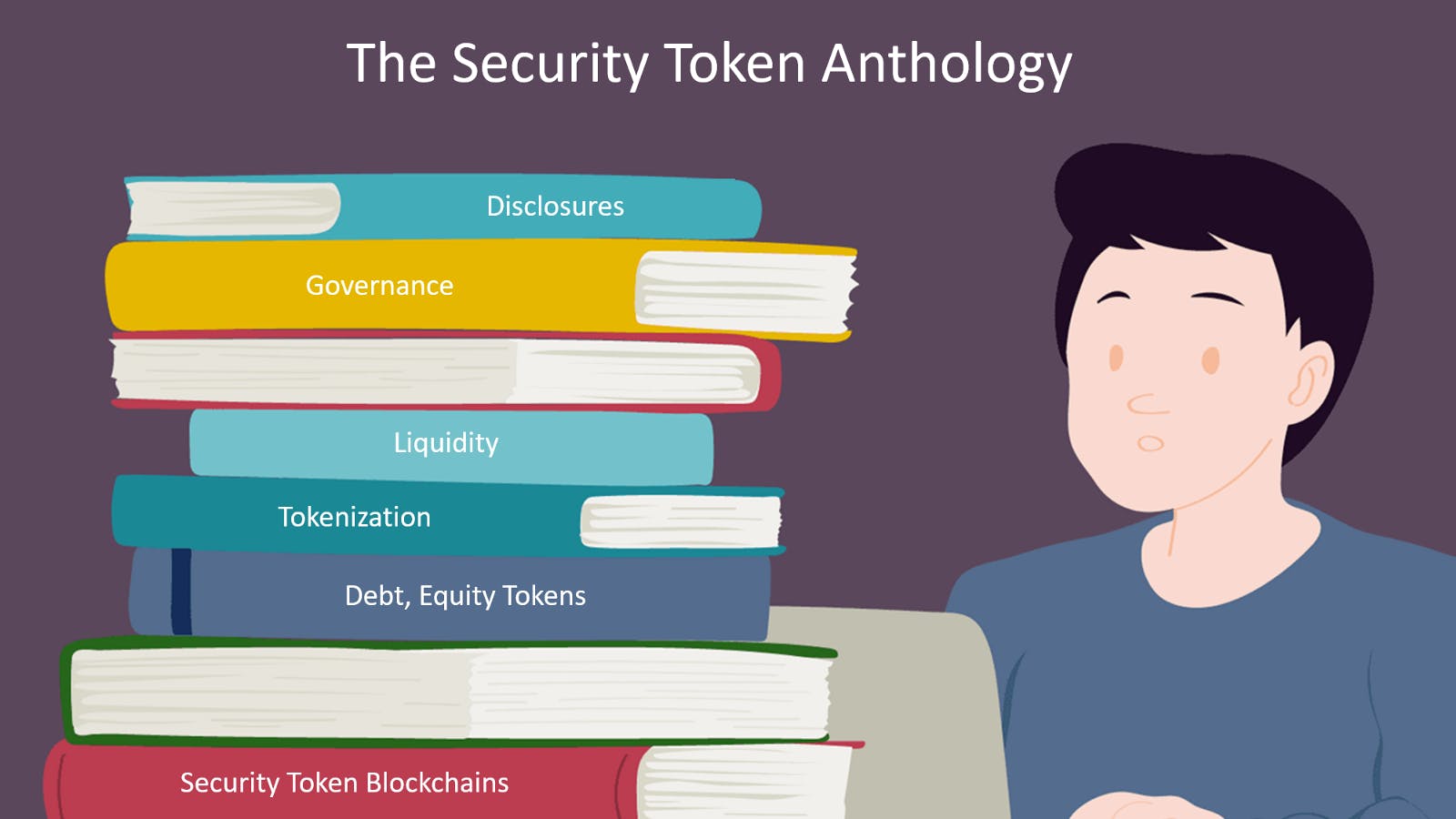
The Security Token Anthology: January 2019 Edition
by
February 14th, 2019
Chief Scientist, Managing Partner at Invector Labs. CTO at IntoTheBlock. Angel Investor, Writer, Boa
About Author
Chief Scientist, Managing Partner at Invector Labs. CTO at IntoTheBlock. Angel Investor, Writer, Boa