864 reads
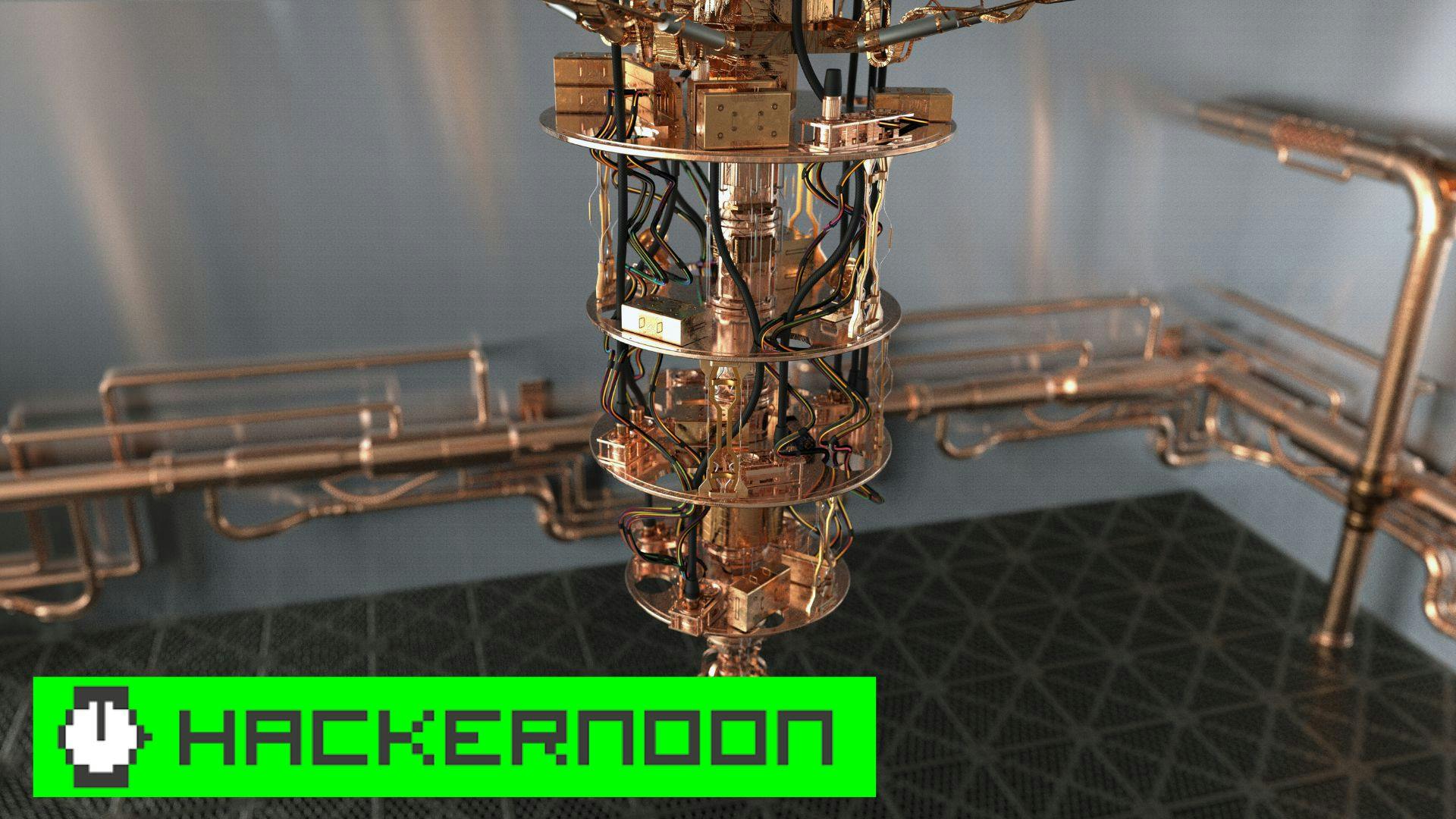
How QANPlatform is solving the White House's Problem of Quantum Attacks
by
March 2nd, 2022

Building and Covering the latest events, insights and views in the AI and Web3 ecosystem.
About Author
Building and Covering the latest events, insights and views in the AI and Web3 ecosystem.